A ransomware attack is one of the most disruptive forms of modern cybercrime. Ransomware is a type of malicious software that prevents users from accessing systems or data until a ransom is paid . In most cases, attackers encrypt victim data or critical files, leaving organizations unable to access important business information unless they pay the ransom.
In many cases, ransomware attacks are delivered through a trojan disguised as a legitimate file, tricking users into downloading or opening malicious attachments. In general, ransomware falls into two primary categories: encrypting ransomware, which encrypts files and demands payment for a decryption key, and non-encrypting ransomware, which locks the victim’s device or operating system. A typical ransomware attack begins when attackers successfully gain access to an organization’s network through phishing emails, exploited vulnerabilities in an operating system, or compromised credentials. Once inside the environment, attackers deploy malicious code that spreads across systems and begins encrypting files across systems and shared storage.
After encryption occurs, victims discover that their files cannot be opened without a unique decryption key controlled by the attacker. The attacker then displays a ransom note demanding ransom in exchange for the decryption key needed to restore the encrypted data.
Over the past decade, ransomware has evolved from relatively simple malware into a highly organized criminal enterprise run by professional ransomware gangs and ransomware operators. These groups conduct large-scale cyber attack campaigns targeting enterprises, government agencies, and critical infrastructure.
Types of Ransomware
Encrypting Ransomware
Encrypting ransomware is the most common type of ransomware attack. This form of malicious software encrypts files such as documents, databases, and backups, preventing victims from accessing their data without the attacker’s decryption key.
Crypto Ransomware
Crypto ransomware is the most common form of ransomware. This type of encrypting ransomware encrypts files such as documents, databases, and backups, rendering them inaccessible without the attacker’s decryption key. Victims typically discover a ransom note demanding a ransom to restore access to the encrypted data.
Non-Encrypting Ransomware
Non-encrypting ransomware does not necessarily encrypt files but instead prevents access to systems or uses extortion tactics to pressure victims into paying a ransom.
Locker Ransomware
Locker ransomware locks users out of the entire operating system instead of encrypting individual files. The infected computer displays a screen preventing access to the system until victims pay the ransom. Although files may remain intact, the device cannot be used until access is restored.
Leakware / Doxware
Leakware / doxware focuses on extortion through data theft. Instead of encrypting files, attackers threaten to publish stolen or sensitive data unless organizations pay the ransom. This tactic is commonly used in double extortion attacks.
Scareware
Scareware uses deceptive alerts and warnings to convince infected users that their systems have been compromised. Victims are pressured into paying a ransom or purchasing fake security software to resolve the supposed threat.
Ransomware Distribution Models
Modern ransomware attacks are frequently enabled through organized cybercriminal ecosystems.
Ransomware as a Service (RaaS)
Ransomware as a service (RaaS) is a criminal business model where ransomware developers create ransomware tools that affiliates can use to deploy ransomware. These affiliates conduct attacks and share ransom payments with the developers. This model has significantly increased global ransomware activity.
Destructive Ransomware Variants
Some ransomware-like attacks are designed primarily for disruption rather than financial gain.
Wipers
Wipers are destructive ransomware variants designed to permanently delete or corrupt a victim’s data. Unlike traditional ransomware, these attacks often aim to cause disruption rather than collect ransom money, making recovery difficult even if victims attempt to pay a ransom.
How a Ransomware Attack Works
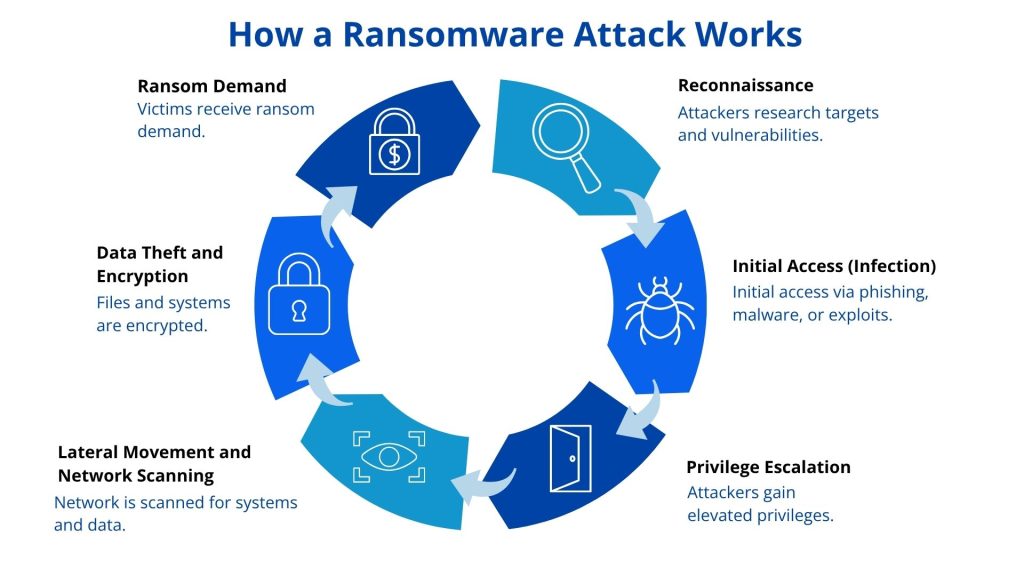
A modern ransomware attack typically unfolds in multiple stages. Although tactics differ between ransomware variants, most attacks follow a similar operational pattern.
1. Reconnaissance
Before launching an attack, ransomware operators often conduct reconnaissance to identify potential targets and weaknesses. Attackers research organizations to understand their infrastructure, employees, and possible vulnerabilities that can be exploited.
2. Initial Access (Infection)
Once a target is identified, attackers attempt to gain entry into the network. Ransomware attackers frequently rely on social engineering attacks or technical vulnerabilities to achieve initial access.
Common entry methods include:
- Phishing emails containing malicious attachment files
- Links to malware delivered through malicious websites
- Exploiting vulnerabilities in outdated operating system software
- Compromised credentials or exposed accounts
- Misconfigured remote desktop protocol services
- Email attachments containing malicious macros
After gaining access, attackers establish persistence within the environment and prepare to deploy ransomware across the network.
3. Privilege Escalation
After gaining an initial foothold, attackers attempt to elevate their privileges to gain broader access within the network. This may involve exploiting system vulnerabilities, stealing administrative credentials, or leveraging misconfigured permissions.
With higher privileges, attackers can move more freely through the environment and prepare the systems for a wider ransomware deployment.
4. Lateral Movement and Network Scanning
During this phase, attackers explore the network to identify valuable systems and sensitive data. They scan connected systems and attempt to spread malware to additional devices.
Attackers often:
- Spread malware to additional systems
- Escalate privileges within the network
- Communicate with a command-and-control server
- Attempt to evade detection by security tools
This stage may occur over several days or weeks before the ransomware infection becomes visible to defenders.
5. Data Theft and Encryption
Modern ransomware groups frequently combine encryption with data theft. This tactic, known as double extortion, significantly increases pressure on victims.
In a double extortion attack, attackers first steal large volumes of sensitive data before launching the encryption phase. The ransomware then scans file directories and storage systems and encrypts critical files using attacker-controlled encryption keys.
Systems affected during this stage often include:
- Shared network drives
- Document repositories
- Application servers
- Employee workstations
- Backup systems
This process can rapidly spread across multiple systems, causing widespread operational disruption.
6. Ransom Demand
Once encryption is complete, attackers deliver a ransom note containing instructions for payment. Victims are typically asked to transfer cryptocurrency in exchange for a decryption key.
Attackers may also threaten to publish stolen data if the ransom is not paid.
Organizations facing these demands must decide whether paying the ransom is advisable . However, many law enforcement agencies advise against paying because it encourages further ransomware activity and does not guarantee successful data recovery.
Even after payment, victims may receive a faulty decryption key, incomplete data recovery, or face additional extortion attempts.
The Evolution of Ransomware
The earliest documented ransomware appeared in 1989 with the first documented ransomware, known as the AIDS trojan. The malware was distributed via floppy disks and demanded payment through postal mail.
The modern era of ransomware accelerated significantly after cryptocurrency allowed attackers to collect anonymous ransom payments.
One of the most significant events in ransomware history was the WannaCry ransomware outbreak in 2017. The attack infected more than 200,000 computers worldwide by exploiting vulnerabilities in the Windows SMB protocol.
Since then, ransomware developers have introduced new delivery models such as ransomware as a service, where cybercriminals can lease ransomware tools without developing their own malware. This model has dramatically increased global ransomware activity.
Today, ransomware groups regularly target healthcare systems, energy providers, and other forms of critical infrastructure, causing large-scale cyber incidents that disrupt essential operations.
The Business Impact of Ransomware
The financial impact of a ransomware attack can be severe. Beyond ransom payments, organizations face operational disruption, regulatory penalties, and recovery costs.
Recent data highlights the scale of the problem:
- The average financial loss from a ransomware attack exceeds $4 million
- Global ransomware payments reached approximately $1.25 billion in 2023
- The average cost of a ransomware breach is around $5.68 million
- In the healthcare sector alone, ransomware caused over $20 billion in losses during 2020
Although fewer organizations now choose to pay the ransom, the volume and sophistication of attacks continue to grow.
How Organizations Can Prevent Ransomware
Preventing ransomware infection requires a layered security strategy focused on limiting access, detecting abnormal activity, and protecting sensitive data.
Organizations can significantly improve ransomware protection by implementing the following measures:
- Regularly update the operating system, applications, and firmware
- Use advanced Endpoint Detection and Response (EDR) tools
- Restrict administrative privileges and limit user permissions
- Deploy application whitelisting to block unauthorized programs
- Disable unnecessary remote desktop protocol services
- Protect remote access with VPNs and multi-factor authentication
- Train employees to recognize phishing and social engineering attacks
In addition, security teams should implement strong data resilience strategies.
Important data protection practices include:
- Maintain regular data backup procedures
- Store backup files offline using the 3-2-1 backup rule
- Implement network segmentation to isolate systems
- Use monitoring tools to detect early ransomware infection behavior
- Isolate infected machines immediately during an active ransomware infection
Organizations should also maintain a detailed incident response plan outlining how to isolate systems, communicate with stakeholders, and restore operations.
Why Ransomware Remains a Growing Threat
Several factors continue to drive the growth of ransomware globally. The rise of ransomware as a service, the availability of cryptocurrency for anonymous ransom payments, and the increasing digitalization of businesses have all contributed to the growth of ransomware activity.
Attackers also continue developing new ransomware variants designed to bypass detection and exploit emerging technologies. As organizations expand cloud adoption, remote work environments, and interconnected supply chains, attackers gain more opportunities to launch large-scale cyber attack campaigns.
Because of these trends, organizations must assume that breaches may occur and focus on limiting damage by protecting sensitive data and restricting attacker movement.
Conclusion
A modern ransomware attack is no longer just a technical malware problem, it is a complex cybercrime operation involving organized ransomware groups, advanced malicious code, and sophisticated extortion tactics such as double extortion.
From early ransomware variants to today’s multi-stage attacks, ransomware continues to evolve in both scale and complexity. Organizations that prioritize strong security practices, proactive detection, and resilient recovery strategies are better positioned to reduce the impact of ransomware infection and avoid the difficult decision of whether to paya ransom.
Protecting sensitive data, enforcing strong access management, and adopting Zero Trust security principles are increasingly critical components of defending against modern ransomware threats.
Ransomware vs Malware
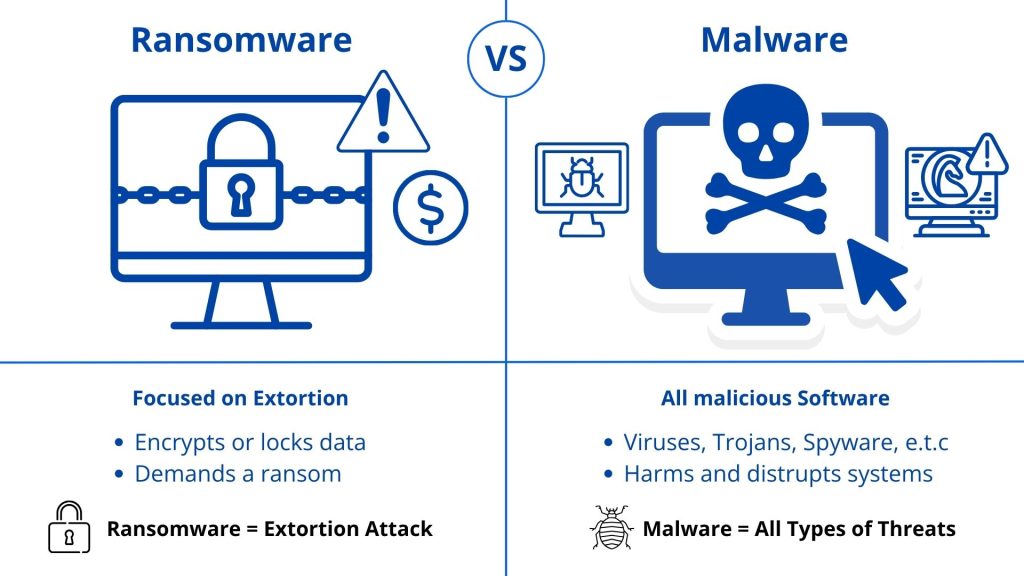
Malware is a broad term that refers to any malicious software designed to damage systems, steal sensitive data, disrupt operations, or exploit networks. It includes threats such as viruses, worms, trojans, spyware, and other forms of malicious code.
Ransomware, however, is a specific type of malware that focuses on extortion. In a ransomware attack, attackers encrypt a victim’s files or lock systems and demand ransom payments in exchange for a decryption key to restore access. While malware can have many different goals, ransomware is primarily designed to generate profit by forcing victims to pay the ransom to regain access to their data or systems.
Learn More About Zero Trust Data Security
For a deeper understanding of how Zero Trust Data Security mitigates ransomware risks and protects critical data, visit our detailed resource page: How Zero Trust Data Security Can Neutralize the Impact of a Ransomware Attack. This page includes best practices, solution features, and real-world examples to help organizations strengthen data protection and ensure business continuity.
FAQ
Ransomware often enters organizations via phishing emails, malicious attachments, or compromised links. Attackers may also exploit unpatched vulnerabilities in operating systems or applications. A data-centric security approach, combined with user training and email filtering, can reduce exposure to these attack vectors.
Immediate steps include isolating infected systems, disconnecting affected devices from networks, and notifying security teams. Maintaining proper offline backups and having a pre-defined incident response plan can limit the impact while enabling safe recovery.
Some ransomware infections can be contained and removed, but encrypted files often remain inaccessible without a decryption key or backup. Using attribute-based access controls and continuous monitoring, organizations can limit damage and prevent ransomware from spreading to other systems.
A layered security approach is most effective. This includes endpoint protection, multi-factor authentication, application whitelisting, and data-centric controls to restrict unauthorized access. Combining Zero Trust principles with proactive monitoring helps prevent both ransomware infection and data exploitation.
The 3-2-1 rule suggests maintaining three copies of critical data, on two separate storage types, with one copy offline. This strategy ensures that even if ransomware encrypts or deletes files, organizations can restore data without paying a ransom.
Prevention focuses on restricting administrative privileges, segmenting networks, regularly updating systems, and training users. Integrating real-time authorization and data-centric security further limits ransomware’s ability to access, encrypt, or exfiltrate sensitive information.
Ransomware attacks have increased globally, targeting sectors like healthcare, finance, and manufacturing. Modern ransomware gangs use double-extortion and ransomware-as-a-service models, making attacks more sophisticated. Organizations that adopt NextLabs Zero Trust Data Security and proactive governance can significantly reduce operational and financial risks.

To comment on this post
Login to NextLabs Community
NextLabs seeks to provide helpful resources and easy to digest information on data-centric security related topics. To discuss and share insights on this resource with peers in the data security field, join the NextLabs community.
Don't have a NextLabs ID? Create an account.