Data Anywhere & Everywhere...
Many enterprises today grapple with managing data beyond networks due to growing data volumes, increased cloud service use, and regulatory compliance, all while minimizing costs. Data must now be stored across multiple locations to optimize performance for advanced computation and ensure redundancy for business continuity in case of disasters. Moreover, data needs to be accessible from anywhere to support global collaboration, remote workforces, and rapid innovation, on top of aiding expansion during M&A and JVs.
Making data readily available has become crucial for staying competitive and achieving faster time-to-market, enabling agile development and CI/CD processes. Consequently, many enterprises resort to the hybrid cloud to preserve business agility and maximize capital investment, ensuring data is accessible to their global workforce, customers, and partners. With new business needs comes the increased demand to deliver services quickly, driving the growth of cloud payload, Gen AI, big data, and analytics. In this new landscape, enterprises must be prepared to handle data everywhere and anywhere.
Implementing a ZTA
Explore in this white paper how to implement a Zero Trust Architecture, along with the impacts on the enterprise, administrator, and end-user when a ZTA strategy is employed.
Why Data-Centric Security(DCS)?
Learn how a data-centric security(DCS) approach can help organizations can maintain the trust of their customers, partners, and stakeholders
What is Dynamic Authorization?
If you’re unfamiliar with dynamic authorization, it could very well be the biggest little secret you’ll hear regarding data security. Explore how dynamic authorization is helping enterprises remain agile.
What is the Most Effective Way to Protect?
As data needs to be protected anywhere and everywhere, regardless of where it resides, whether on-premises, in the cloud, or in transit while ensuring that data remains protected in use independent of the device or network accessing it, security efforts to secure data should be centered on protecting data itself (data-centric), instead of the systems or networks where data is kept (network-centric). A conventional perimeter-based approach that focuses on securing access to a network is no longer sufficient to protect data because with global workforce, remote work, and move to cloud and hybrid environments, it is becoming too complex and costly to clearly defined perimeter between secure and insecure zones.

Moreover, it is imperative to make data available and easily accessible to both internal and external stakeholders including employees, customers, and supply chain partners. This means enterprises need to ensure data shared and transmitted to internal users as well as to third party users outside of the corporate network remains secure regardless of who & what is accessing it and how, where, and when it is accessed.
Since potential threats can originate either inside or outside of secure networks, every access and use of data must be verified and granted at the time of request. This is done on a need-to-know basis following least privilege principle, while monitoring access continuously with detailed logs to support audits and forensic investigations.
Zero Trust Data-Centric Security
Protecting data comprehensively, whether it is at rest, in transit, or in use, across all the systems where data is managed, requires a multi-layered and policy-driven approach that incorporates a variety of data-centric security (DCS) controls to protect data which include access control, data obfuscation, data segregation, digital rights management (DRM), and data loss prevention.
These security controls need to be enforced dynamically in real-time based on centrally managed policy. Data security policies must evolve as factors change that impact who and what is authorized to access a particular set of data, without manual intervention.

These security controls need to be enforced dynamically in real-time based on centrally managed policy. Data security policies must evolve as factors change that impact who and what is authorized to access a particular set of data, without manual intervention.
Zero Trust Architecture (ZTA) assumes no perimeter and requires every access request to be verified, this suits well for the needs of protecting data everywhere and anywhere. The policy-based and identity centric approach of ZTA to security based on least privilege principle has received widespread corporate adoption and recognized by governments and regulatory bodies including US federal government, NIST, and most large corporations as the security architecture of the future. By adopting an approach that combines data centric security (DCS) with zero trust architecture, organizations can ensure continuous protection of their data throughout its lifecycle across all environments.

Zero Trust Architecture (ZTA) assumes no perimeter and requires every access request to be verified, this suits well for the needs of protecting data everywhere and anywhere. The policy-based and identity centric approach of ZTA to security based on least privilege principle has received widespread corporate adoption and recognized by governments and regulatory bodies including US federal government, NIST, and most large corporations as the security architecture of the future. By adopting an approach that combines data centric security with zero trust architecture, organizations can ensure continuous protection of their data throughout its lifecycle across all environments.
Zero Trust Data-Centric Security is an approach which combines zero trust principles and data-centric security (DCS) to create a comprehensive security strategy that puts the data that needs to be protected, at the center of an organization’s data security efforts. Zero trust can help to limit access to sensitive data through least privilege access, while data-centric security (DCS) protects the data itself. With this approach, organizations can implement need-to-know access, segregate data, securely collaborate with persistent data protection, unify access control with ABAC, and externalize access management to eliminate security silos and protect against threats that can originate inside or outside of an organization.
Key Components
Attribute Based Access Control (ABAC)
Authorize subject requests to perform operations on objects based on assigned attributes of the subject and object, environment conditions, and a set of policies that are specified in terms of those attributes and conditions.
Dynamic Authorization Policy Engine
Evaluate attribute-based policies at the time of access to grant permission based on least privilege, a core component of Zero Trust Architecture to ensure the principle of never trust, always verify.
Centralized Policy Management
Define and author access control and data protection policies through a centrally managed interface, so they can be applied consistently across the entire enterprise wherever data is being accessed and used.
Real Time Policy Enforcement
Enforce need to know access and data security policies based on user identity, the current value of subject attributes, object attributes, and environment conditions to protect data in use, at rest, and in motion.
Centralized Monitoring & Audits
Track real-time user and data access activities across apps and services in a central repository, simplify the process of monitoring user access, automating compliance reporting, and detecting potential threats.
NextLabs Approach
An organization’s data protection is only as strong as its weakest link, so data security policies must be consistent across the entire enterprise and enforced dynamically at the time of data access to ensure they are always up to date. In addition, when collaborating with external partners organizations need to ensure their data protection policies are still enforced. All these policies need to be kept up to date with any changes in factors that affect who is authorized to access protected data.
NextLabs products enable organizations to protect their data, anywhere and everywhere. Our products use a Zero Trust data-centric approach to dynamically enforce data security policies, protecting data whether it is at rest, in use, or on the move. Data is protected within applications as well as in structured and unstructured data stores through NextLabs’ unified data security policy platform, providing a Zero Trust Architecture (ZTA) for organizations. Our dynamic authorization technology and real-time policy engine allows data access policies to be enforced at the time of access, wherever the data is being accessed.
Zero Trust Data Security
NextLabs Zero Trust Data Security is a comprehensive data centric security (DCS) solution based on zero trust architecture to enforce access rights and protect structured and unstructured data throughout its entire lifecycle: at rest, in transit, and in use; regardless of where data resides – whether it is in application, file, file repository, or database on-premises, or in the cloud.
-
CloudAz
Unified policy management platform with Dynamic Authorization Policy Engine.
-
SkyDRM
Persistent protection of critical files and documents stored and shared anywhere.
-
Application Enforcer
Secure applications, externalize entitlement, protect data, and simplify access management.
-
Data Access Enforcer (DAE)
Zero Code approach to secure access and protect critical data independent of application.
Core Functionalities
Dynamic Authorization and Zero Trust Architecture (ZTA)
Technology leader with 90+ patents and an official member of the NIST National Cybersecurity Excellence Partnership program since its inception.
Highest Performant and Most Scalable Policy Engine
The most mature & battle-tested policy engine in the industry processing greater than 10 billion authorization requests per year.

Comprehensive Data-Centric Security (DCS)
Protect structured and unstructured data throughout its entire lifecycle: at rest, in transit, and in use; to ensure end to end secure data pipeline regardless of where data resides – whether it is in application, file, file repository, or database on-premises or in the cloud.
Externalized Authorization
Modify access and authorization policies centrally across the entire enterprise without having to make changes within each application.
Real-time Data Masking and Segregation
Data segregation and obfuscation policies that can be enforced dynamically at the time of the data access request ensures that protected data is only accessed by those who are authorized.
Native Application Integrations
Out-of-the-box, zero-code integrations with 100s of enterprise and business applications allow for quick and easy deployments and fast time to value.
Next Generation Technology
Cloud native and container-based unified policy platform and enforcers enable rapid multi and hybrid cloud deployment with the best time-to-value track record.

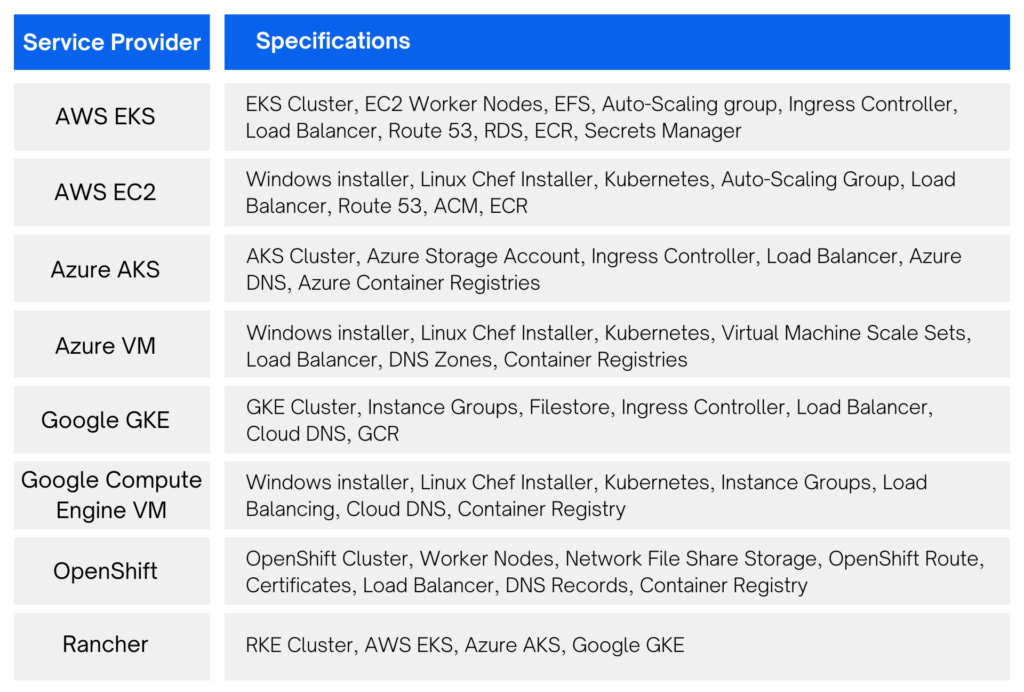
Run on any Cloud
Enterprises often have a combination of on-premises and across multiple cloud environments and need a single solution to protect data everywhere.
NextLabs products can be deployed anywhere, be it on-premises, in private cloud, or as a SaaS. Our products run natively on AWS, Azure, OpenShift and Google Cloud. With support for multiple deployment models, it gives you the freedom to choose the right cloud deployment strategy, whether it is hybrid or multi-cloud.
SaaS
Private Cloud

On-Premise
Consistent Policies
Whatever the environment, the NextLabs Zero Trust Data-Centric security suite of products allows organizations to apply data access policies to all of their data across the organization.
All Lifecycle Stages
Data is always protected, at rest, in use, and on the move, whenever and wherever it is being accessed.