In the age of digital transformation, organizations strive to become 21st century digital enterprises by securing the following objectives:
- Unify Business Processes: Synchronize disparate business operations to improve efficiency and enable seamless interactions between departments
- Consolidate Infrastructure: Streamline infrastructure to simplify management and reduce maintenance costs
- Modernize IT: Update and innovate IT systems with new technologies such as machine learning and big data analytics
- Accelerate Collaboration: Promote faster collaboration across departments and geographies, fostering innovation and quicker decision-making
- Cloud Adoption: Foster a flexible and resilient IT infrastructure, scale resources to meet ever-changing business demands.



Closing the Digital Divide
However, most organizations are still facing obstacles in their digital transformation – the process of digitization has created un-ignorable security gaps that need to be addressed. Closing the digital divide is an imperative step to ensure organizations can navigate the cyber landscape with confidence and resilience.
Companies should thus prioritize these key operations in data security:
01
Zero Trust
Continuous authorization of all access attempts, prioritize data protection over network boundaries
02
Automation
Automate data security and internal controls to eliminate human error and enhance business integrity
03
Prevention
Shift from manual detective controls to automated preventive controls to optimize threat detection
04
Smart Audit
Track and monitor all access activity, use risk analytics to correlate, identify and alert on anomalies
05
Cloud Native
Seamlessly integrate security solutions with business infrastructure for quick time-to-value

What can enterprises do?
As data security requirements continue to evolve, organizations encounter various business hurdles, all while striving to close the digital divide:
-
CybersecurityCybersecurity
Safeguard data against unauthorized users with compromised credentials and administrative access across the cloud
-
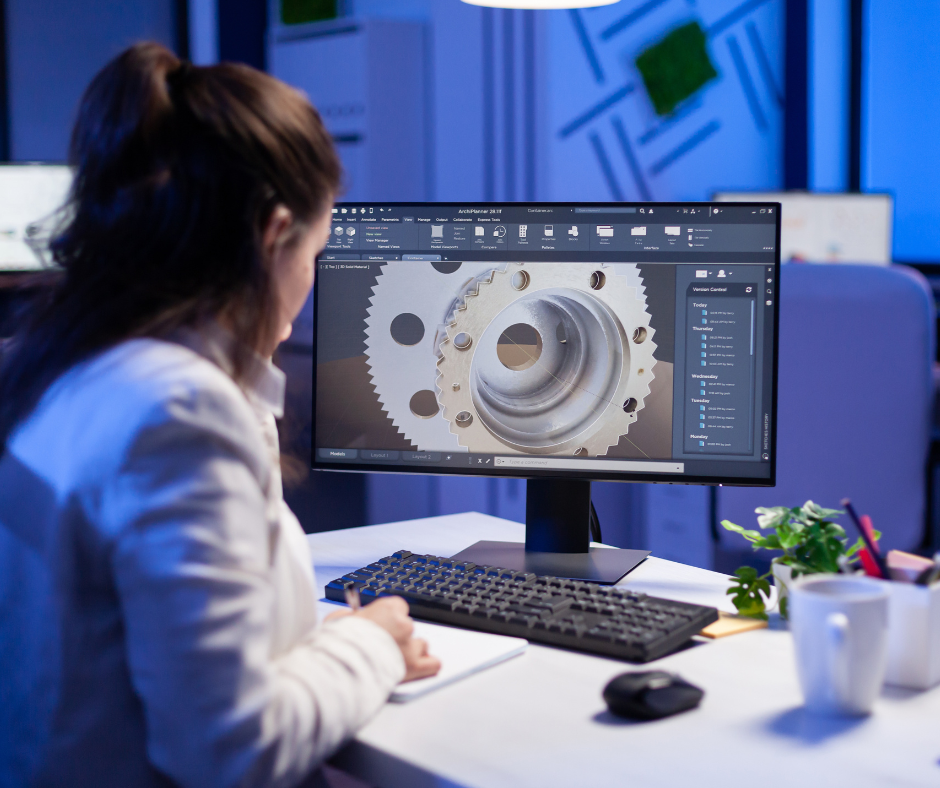
Digital TransformationDigital Transformation
Preserve business continuity, data security and integrity during ERP consolidation and data migration projects
-
Merger & AcquisitionsMerger & Acquisitions
Segregate sensitive information in shared system to safeguard IP and data privacy, address increased cybersecurity risks during the IT change gap
-
Regulatory ComplianceRegulatory Compliance
Keep up with complex regulatory environments across global operations, managing time-intensive audit processes
-
Secure CollaborationSecure Collaboration
Balance the need to share data internally and externally with the need to protect sensitive information from unauthorized access and data breaches
-
Trade SecretTrade Secret
Protect intangible assets from increasingly sophisticated cyberattacks, corporate espionage and insider threats
Implementing Zero Trust Data Security
Businesses require a data security solution that can fulfill 21st century enterprise objectives. This can be achieved through a unified policy platform that combines zero trust, automation, prevention, smart audit and cloud-native operations.
The unified policy platform should focus on these key areas:
- Policy Governance – Users author security policies that are automatically enforced across the entire organization, with approval workflow, policy rollback and audit features
- High Performing Policy Engine – Dynamically evaluates access requests against attribute-based policies and prevents unauthorized access
- Application-native Enforcement – Policies are implemented by comprehensive enforcement solutions across different data enclaves, from files to databases, through native integration
- Cloud Deployment – Integrates with existing cloud infrastructure and business processes
NextLabs Zero Trust Data-Centric Security
Secure the Digital Enterprise
By implementing a zero-trust data-centric security solution, businesses can finally secure their transformation into a digital enterprise and achieve these outcomes:
Preserve Business Continuity: Safeguard data without disrupting existing business workflow, ensure secure transition from traditional business models to digitized versions
Strengthen Security & Compliance: Prevent data breaches and wrongful disclosure, simplify audit processes and ensure regulatory compliance
Increase Collaboration & Availability: Ensure secure sharing with high data availability to accelerate collaboration
Automate Operations: Accelerate time to market and enhance competitive advantage through automation of business processes