Home | Intelligent Enterprise | Zero Trust Architecture | What is Policy and Access Visibility in Zero Trust Security?
Modern security threats exploit gaps in visibility and inconsistent access controls, allowing attackers to move laterally and access sensitive data. To address this, many organizations adopt a Zero Trust architecture built on continuous monitoring, contextual analytics, and dynamic policy enforcement. Visibility and analytics enable the observation of network traffic, evaluation of user behavior, and detection of threats to guide security decision-making.
Visibility and Analytics in the Zero Trust Model
The Visibility and Analytics Pillar
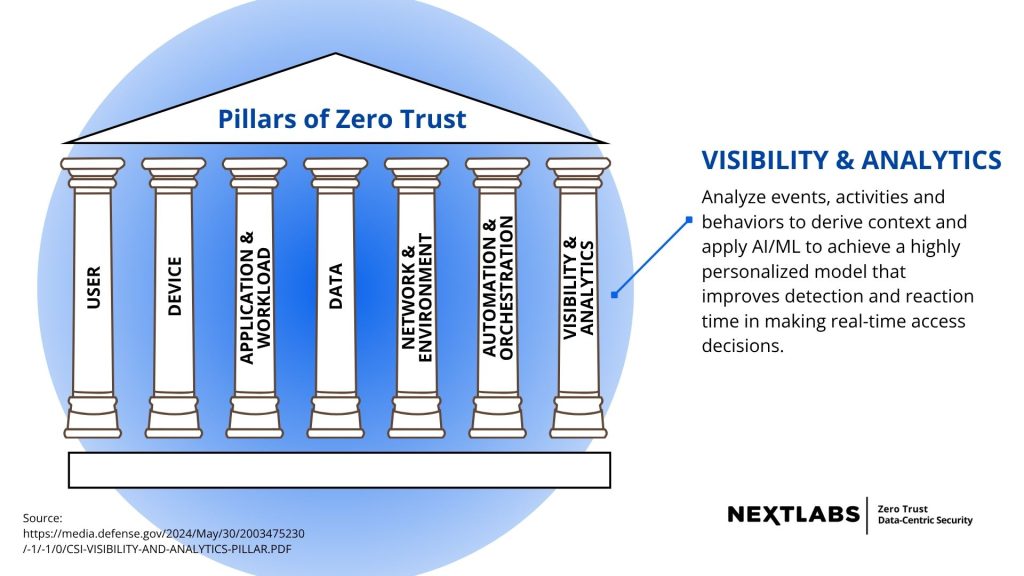
Within a zero trust architecture, the visibility and analytics pillar provides a strategic framework for collecting and interpreting enterprise security information. The pillar focuses on aggregating telemetry from users, devices, applications, and network infrastructure to enable comprehensive analysis of enterprise activity.
Through centralized visibility and analytics, organizations can observe network traffic, track user access, and monitor network resources in real time. This aggregated data supports threat hunting, anomaly detection, and risk-based policy decisions. The analytics pillar also allows organizations to correlate telemetry from multiple sources, identify abnormal network activity, and detect previously unseen threats.
Supporting Trust Maturity
The visibility and analytics pillar also supports the progression of trust maturity within a zero trust model. As organizations expand their ability to observe network activity and analyze behavior, they improve their ability to validate access decisions and detect malicious activity. Continuous monitoring and analytics enable organizations to make real-time security decisions based on operational data, improving the effectiveness of enterprise security controls and aligning with the Zero Trust Maturity Model.
Logging and Observing Security Activity
Logging Security Events Across the Enterprise
Logs may originate from networks, devices, applications, and cloud systems. Aggregating and analyzing these logs provides a comprehensive view of enterprise activity and helps detect suspicious behavior.
Centralized Security Information and Event Management
Security Information Platforms
Centralized event management platforms enable organizations to aggregate security information from across enterprise networks and systems. For example, modern security information and event management (SIEM) platforms function as scalable systems capable of collecting telemetry from network infrastructure, endpoint devices, and enterprise cloud services. Through centralized visibility and analytics, such platforms help organizations monitor security events, perform analysis, and detect potential security threats.
Security and Risk Analytics
Risk-Driven Security Analysis
Organizations use analytics to evaluate risk across enterprise systems, network assets, and data resources. This analysis combines information about vulnerabilities, system configurations, and known security threats. Risk-driven analytics help organizations prioritize security events, identify critical assets, and determine the potential impact of security incidents. By incorporating threat intelligence and vulnerability information, organizations can develop more accurate risk assessments and strengthen the enterprise security posture.
Actionable Insights for Security Teams
Through advanced analysis, organizations can transform raw data into actionable insights that guide security decision-making. These insights help security teams understand evolving threats, prioritize incident response, and improve threat hunting operations.
Network Visibility Across Modern Infrastructure
Expanding Network Visibility
Achieving strong network visibility requires comprehensive monitoring across enterprise infrastructure. Many organizations operate across hybrid environments that combine on-premises systems, cloud platforms, and distributed devices. Improving network visibility may involve deploying additional network monitoring tools that capture telemetry across enterprise networks.
Enhanced network visibility enables security teams to:
- Analyze network traffic
- Monitor network resources
- Detect suspicious traffic
- Identify unauthorized devices
Monitoring Encrypted Traffic
A growing percentage of enterprise network traffic is encrypted, which can limit traditional inspection methods. However, understanding patterns in encrypted traffic remains essential for identifying potential security threats. Security operations centers require tools capable of analyzingencrypted network traffic to detect anomalies without exposing sensitive data. By analyzing metadata and traffic patterns, organizations can detect suspicious behavior, identify command-and-control activity, and enhance threat detection.
User and Entity Behavior Analytics
Behavioral analytics examines patterns of user and device activity across the networks, applications, and endpoints. By establishing normal behavioral baselines, it can identify deviations that may indicate compromised accounts, insider threats, or other suspicious activity. This insight allows security teams to respond proactively before small anomalies escalate into serious breaches.
Threat Intelligence Integration
Integrating threat intelligence into visibility and analytics provides context about known adversary tactics, techniques, and vulnerabilities. This contextual information helps security teams prioritize alerts, focus on the most critical threats, and improve the accuracy of threat detection and response across the enterprise.
Monitoring Devices and Operational Technology
Continuous monitoring of all devices, including endpoints, IoT, and operational technology ensures that every connected system is visible to security teams. This reduces hidden risks, helps identify unauthorized devices, and supports policy enforcement, allowing organizations to maintain secure operations across complex, distributed environments.
Policy and Access Visibility in Zero Trust
Centralized Identity and Access Control
Organizations can improve access visibility by transitioning to a zero trust framework that emphasizes continuous monitoring and automated policy enforcement. Centralized Identity and Access Management (IAM) systems allow organizations to manage user access, enforce least-privilege policies, and strengthen enterprise security across distributed environments. Implementing phishing-resistant multi-factor authentication (MFA) further strengthens security by protecting authentication processes and preventing credential misuse.
For automated enforcement and dynamic policy decisions, leveraging the CloudAz policy platform helps ensures consistent policy application across systems and environments.
Preventing Policy Drift
Centralizing policies prevents policy drift, where different environments enforce inconsistent security controls. Consistent policy enforcement improves governance and strengthens enterprise security management practices. Real-time visibility into user access ensures that organizations can evaluate risk, monitor policy enforcement, and respond quickly to suspicious events.
Continuous Monitoring and Compliance
Continuous visibility and monitoring play an essential role in regulatory compliance and enterprise security operations. Organizations that implement strong visibility and analytics capabilities can generate audit records, track user activity, and maintain tamper-resistant compliance logs. Continuous monitoring also enables organizations to demonstrate compliance with privacy regulations, such as GDPR and HIPAA by actively monitoring data access and policy enforcement.
Advancing Trust Maturity Through Visibility and Analytics
The implementation of the visibility and analytics pillar supports informed security decisions across the enterprise. By combining strong network visibility, behavioral analytics, and centralized security information, organizations gain a deeper understanding of enterprise operations. As organizations advance their trust maturity, visibility and analytics capabilities allow them to detect threats, reduce risk, and respond more effectively to emerging cyber threats.
Through continuous monitoring, advanced analytics, and policy-driven access control, organizations can build resilient zero trust architectures capable of protecting sensitive data, systems, and enterprise networks.
Conclusion
Implementing strong policy and access visibility within a Zero Trust framework enables continuous monitoring, anomaly detection, and rapid threat response, building a resilient, risk-aware enterprise security posture.
NextLabs Resources
- What is Policy and Access Visibility in Zero Trust Security?
- Visibility and Analytics in the Zero Trust Model
- Logging and Observing Security Activity
- Centralized Security Information and Event Management
- Security and Risk Analytics
- Network Visibility Across Modern Infrastructure
- Monitoring Encrypted Traffic
- User and Entity Behavior Analytics
- Threat Intelligence Integration
- Monitoring Devices and Operational Technology
- Policy and Access Visibility in Zero Trust
- Continuous Monitoring and Compliance
- Advancing Trust Maturity Through Visibility and Analytics
- Conclusion
- Resources






