Organizations across industries are rethinking how they approach cybersecurity. Traditional perimeter-based defenses were designed for environments where systems, users, and data remained inside a defined network. Today’s distributed infrastructure including cloud platforms, remote users, third-party partners, and mobile devices requires a fundamentally different approach.
The Zero Trust Maturity Model (ZTMM) provides a strategic framework for organizations to transition from traditional security practices toward a modern Zero Trust architecture built on continuous verification. Rather than assuming internal resources are inherently secure, Zero Trust treats trust as a vulnerability, requiring that every request for access be verified based on identity, context, and risk
By applying ZTMM, organizations can assess their current cybersecurity maturity, identify gaps in access control and security policies, build phased implementation plans, and measure progress across multiple capabilities. The goal is to prevent unauthorized access to data, services, and systems while improving the organization’s overall security posture over time.
Why the Zero Trust Maturity Model Matters
Cyber threats continue to evolve in both scale and sophistication. According to IBM, the average cost of a data breach exceeded $4.8 million in 2024, highlighting the importance of improving security practices. While 81% of companies pursue some form of a zero trust strategy, most organizations struggle to implement it effectively.
Zero Trust is not a single technology; it is a collection of trust principles, architectural concepts, and operational practices that must be implemented across multiple systems, users, devices, and workloads. The Zero Trust Maturity Model addresses this complexity by providing:
- A roadmap to evaluate security capabilities
- A structured path to implement Zero Trust controls
- A method to measure zero trust maturity across the enterprise
By using the model, organizations can transition from static, perimeter-based defenses to a dynamic and risk-aware architecture.
The Role of CISA in the Zero Trust Maturity Model
The Cybersecurity and Infrastructure Security Agency (CISA) developed the CISA Zero Trust Maturity Model to help federal agencies modernize cybersecurity posture. While initially designed for government agencies, the framework is flexible enough to support organizations across industries with varying business needs, operational constraints, and production environments.
The CISA model enables organizations to assess their current cybersecurity posture, identify gaps through gap analysis, develop practical trust strategies, and build long-term zero trust plans. Organizations interested in detailed implementation approaches can also explore the NextLabs approach to CISA’s Zero Trust Maturity Model (ZTMM).
The Five Pillars of the CISA Zero Trust Maturity Model
The CISA ZTMM organizes security capabilities into five pillars, each representing a critical component of modern trust architecture:
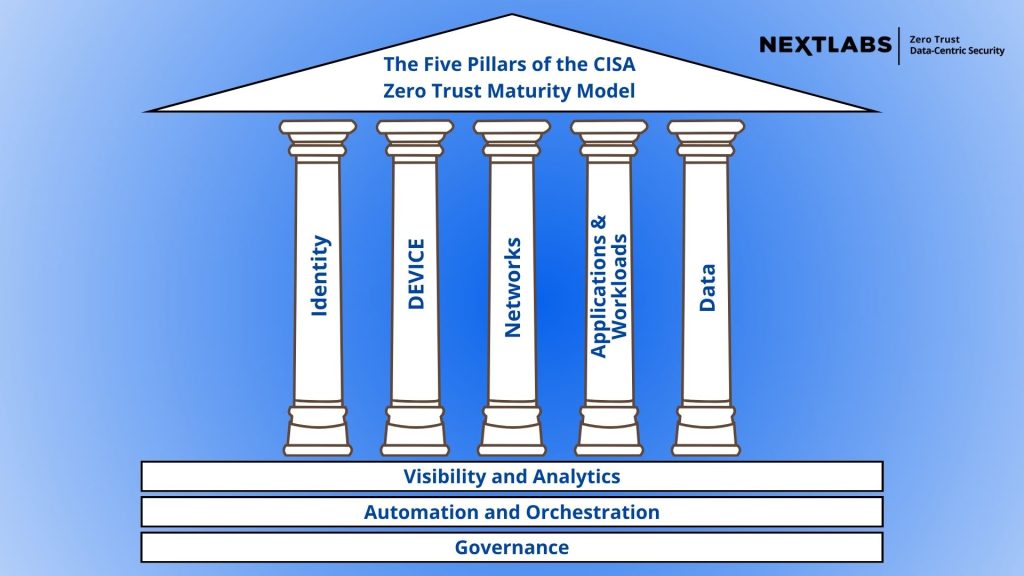
Identity
Identity verification is fundamental to Zero Trust. Organizations must ensure that users, services, and applications are authenticated before granting access. Strong identity management involves multi-factor authentication (MFA), identity lifecycle management, risk-based authentication, and least-privilege access control.
Devices
Devices accessing systems and data must be secure and compliant. This includes monitoring device health and configuration, assessing endpoint detection capabilities, confirming device ownership and trust status, and ensuring secure device onboarding. These controls reduce risks from unmanaged devices, compromised endpoints, and malicious threat actors.
Networks
Zero Trust architecture limits lateral movement and secures network traffic. Key practices include network segmentation, secure access policies, micro-segmentation of assets, and encryption of traffic. Unlike traditional perimeter-only approaches, these measures enforce granular security controls across the network.
Applications and Workloads
Applications and workloads must authenticate identities, enforce consistent security policies, and monitor behavior aligned with zero trust objectives. Secure development practices ensure that applications are designed for a Zero Trust environment from the outset.
Data
Protecting sensitive data is the cornerstone of Zero Trust. Organizations classify data, encrypt it at rest and in transit, govern access, and monitor usage continuously. A mature architecture secures data regardless of location, whether on-premises, in the cloud, or across partner environments.
The Three Cross-Cutting Capabilities
Supporting all five pillars are three cross-cutting capabilities that enable enterprise-wide Zero Trust:
- Visibility & Analytics: Provides insights into who accessed what, when, from where, and using which devices. This capability is critical for continuous monitoring, improved threat detection, and rapid response.
- Automation & Orchestration: Transforms static policies into dynamic enforcement mechanisms, enabling automated policy application, threat response, and workflow orchestration across systems.
- Governance: Ensures that security decisions align with business needs, regulatory requirements, and organizational strategy. Strong governance defines trust objectives, maintains accountability, and enforces consistent security policies.
Maturity Stages in the Zero Trust Maturity Model
Each pillar evolves through four maturity stages:
- Traditional: Relies on perimeter-based security, static policies, manual configurations, and limited visibility. Implicit trust within the network exposes systems to risk.
- Initial: Organizations begin implementing basic automation for identity and device management, least-privilege access, and early visibility into network activity.
- Advanced: Features centralized identity management, policy integration across pillars, near real-time visibility into security risks, and automated enforcement of security policies.
- Optimal: Achieves fully automated policy-based access control, dynamic risk-based enforcement, automated threat detection, and continuous verification of identities, devices, and network traffic.
Implementing the Zero Trust Maturity Model
Successfully adopting the model requires careful planning and phased implementation:
- Assess Current Maturity – Evaluate the organization’s maturity across the five pillars and three cross-cutting capabilities, often through a gap analysis.
- Define Objectives and Priorities – Establish zero trust objectives and prioritize investments based on business risk and operational impact.
- Develop a Phased Roadmap – Gradually implement Zero Trust capabilities across systems, networks, and data environments.
- Run Pilot Programs – Test assumptions and measure progress before broader rollout, such as enforcing least-privilege access or monitoring network anomalies.
- Continuously Monitor and Optimize – Maintain continuous monitoring and refine security policies as identities, applications, and devices evolve.
The Cultural Shift Required for Zero Trust
Zero Trust implementation is not purely technical; it requires organizational change. Security practices, governance, operational processes, and cross-team collaboration must adapt to support a zero trust strategy. Alignment between IT teams, security leaders, and business stakeholders is essential for success.
Moving Toward a Mature Zero Trust Architecture
The CISA Zero Trust Maturity Model offers a practical roadmap for strengthening cybersecurity and protecting critical assets. By assessing current maturity, aligning trust strategy with business needs, and implementing capabilities across the five pillars and three cross-cutting capabilities, organizations can build a resilient, adaptive architecture. Over time, improved visibility, automated security enforcement, and strong identity-based access control help reduce risks, prevent unauthorized access, and protect sensitive data across complex environments.
In summary: The zero trust maturity model enables organizations to transition from traditional perimeter defenses toward a fully automated, identity-driven, and data-centric security

To comment on this post
Login to NextLabs Community
NextLabs seeks to provide helpful resources and easy to digest information on data-centric security related topics. To discuss and share insights on this resource with peers in the data security field, join the NextLabs community.
Don't have a NextLabs ID? Create an account.