As sensitive data flows continuously across regions, systems, and organizational boundaries, the regulatory landscape governing it has grown more complex and overlapping. Most organizations still respond to compliance reactively — addressing each new regulation in isolation — producing fragmented tooling, inconsistent controls, and limited visibility. This paper argues for a holistic model built on three shared compliance threads present across virtually all major regulations: automating access controls, preventing wrongful disclosure, and automating audit and reporting.
The Compliance Challenge
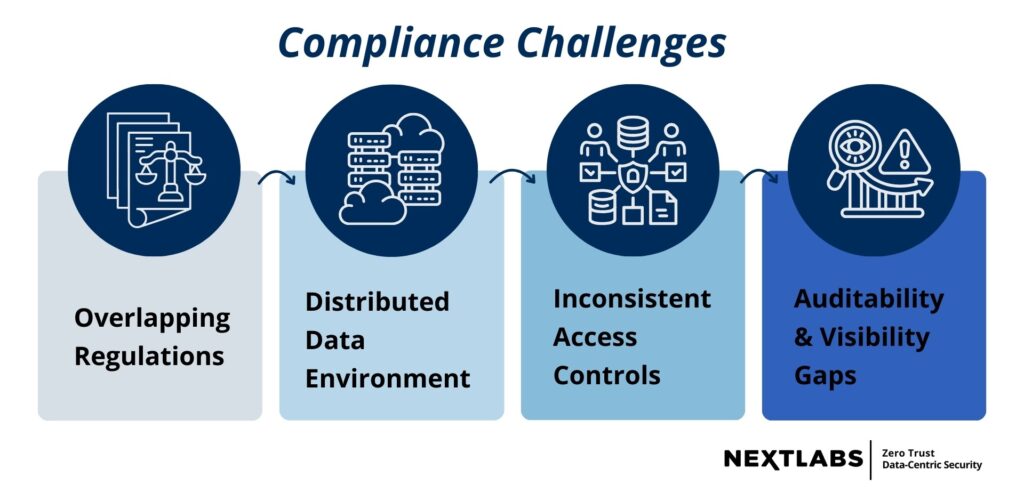
Enterprises face an expanding array of regulatory requirements including HIPAA, ITAR, DFARS, CMMC, SOX, and emerging AI governance standards, yet many continue to address them reactively. IBM’s 2025 analysis puts the average cost of a data breach at USD 4.4 million — a figure that reflects legal exposure, operational disruption, and reputational damage alongside technical recovery. Addressing each regulation as a standalone obligation compounds the problem, producing a patchwork of tools with duplicated effort, unclear ownership, and increasingly difficult-to-sustain security architecture.
The Intersection of Compliance and Data Security
Compliance and data security are distinct disciplines with different priorities, but they depend on the same underlying controls: access management, encryption, audit logging, and incident response. In most organizations, however, they are managed by separate teams — legal and audit on one side, security and IT on the other — producing implementations that solve one regulation or one system at a time. Treating this overlap as an opportunity rather than a friction point is where a more sustainable strategy begins.
Driving the Need for a Holistic Approach
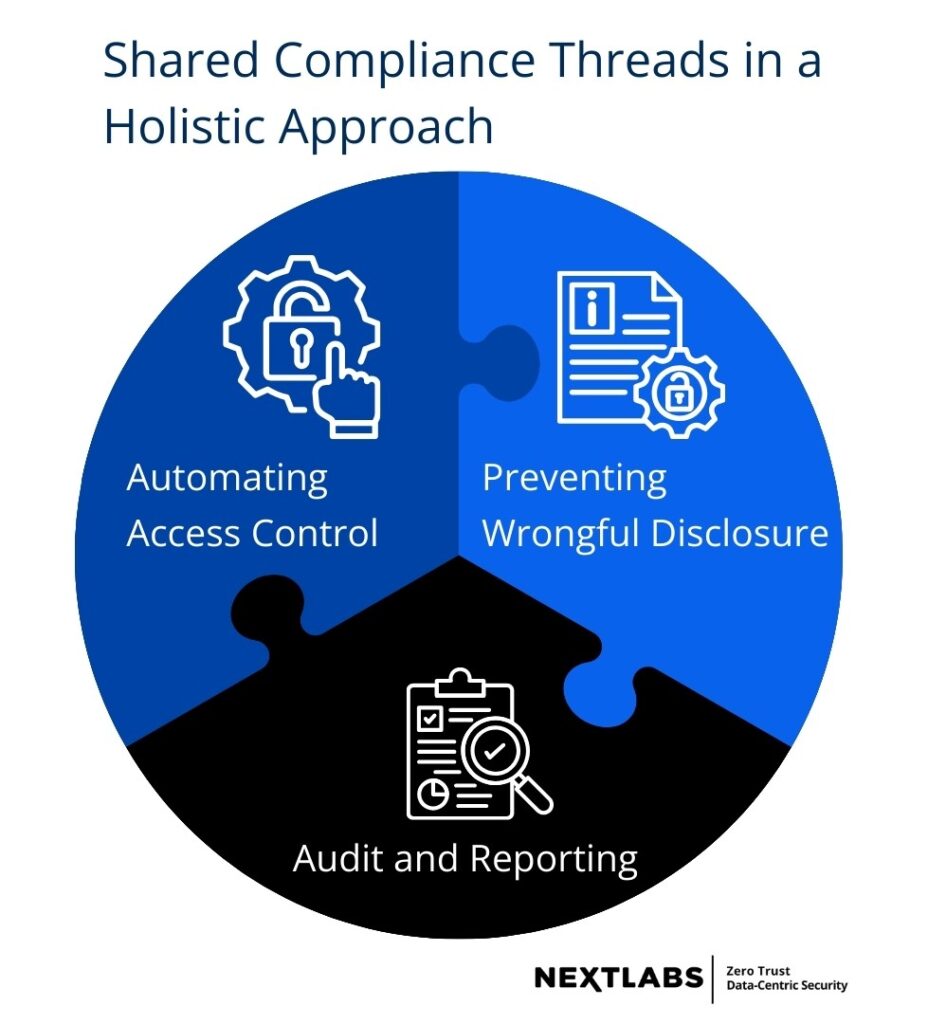
A holistic approach manages regulatory compliance and data protection through a single unified control model rather than regulation-by-regulation implementations. Because sensitive data is often subject to multiple regulatory requirements simultaneously, it must be governed consistently across systems, users, and workflows. Across major frameworks — GDPR, CCPA, DFARS, CMMC, SOX, EAR, ITAR, and HIPAA — three recurring compliance threads emerge:
- automating access controls
- preventing wrongful disclosure
- maintaining audit and reporting capability
By anchoring compliance to these shared threads, organizations can apply protection mechanisms once and extend them across regulatory domains — reducing duplication while still respecting regulation-specific constraints.
Case Studies of Success and Failure
The contrast between a holistic and fragmented approach plays out clearly in practice. A multinational aerospace and defense manufacturer subject to ITAR, EAR, DFARS, CMMC, and GDPR adopted a unified, policy-driven model — enforcing each regulation through shared access control, filtering, and audit mechanisms. When requirements changed, policies were updated centrally. Audits produced fewer findings, compliance costs fell, and visibility improved.
A global financial institution managing SOX, GDPR, and CCPA through separate teams and systems fared differently. Controls were inconsistently applied as data moved between platforms, and following a data exposure incident, the organization could not demonstrate consistent enforcement — resulting in regulatory penalties and mandated remediation. Regulatory complexity was equal in both cases. The difference was entirely in approach.
The Shift Toward Zero Trust, Data-Centric Security
Zero Trust provides the strategic framework best suited to modern regulatory demands. By operating on the principle of “Never Trust, Always Verify” and enforcing least-privilege access at every interaction, it aligns naturally with the access control requirements found across most regulatory frameworks. Data-centric security extends this further, ensuring that protection travels with the data itself regardless of where it resides or who is accessing it. Together, they shift compliance enforcement from static, perimeter-based controls to adaptive, policy-driven decision-making — and a centralized policy platform is what makes this scalable.
Turning Policy Into Practice
The operational model translates each regulation into its own policy set while enforcing all of them through a single platform. This separates policy definition from enforcement, preventing compliance logic from becoming buried in individual applications and making it possible to update or retire policies as regulations evolve. Supporting technologies operationalize this at the data level: fine-grained access control and data segregation enforce least-privilege at the point of access; data filtering, masking, and Digital Rights Management ensure sensitive information is protected wherever it travels; and centralized audit logging provides the visibility needed to demonstrate compliance across frameworks simultaneously.
NextLabs Solution for Regulatory Compliance
NextLabs translates diverse regulatory requirements into enforceable, context-aware policies through a unified, data-centric platform.
- CloudAz provides centralized authoring and management of attribute-based Zero Trust policies. Powered by NextLabs’ patented Dynamic Authorization Policy Engine, CloudAz evaluates access requests in real time and records all decisions in a centralized audit repository.
- Application Enforcer enhances existing applications with fine-grained access controls and data protection, without requiring custom code changes. It enables organizations to extend security consistently across enterprise applications and services.
- Data Access Enforcer (DAE) delivers data-level security controls independent of user interface, APIs, or applications. It enforces global data segregation, masking, and access policies at scale.
- SkyDRM provides persistent protection and usage control for unstructured data and files. It ensures that sensitive documents remain protected regardless of where they are stored or shared.
Conclusion
Reactive, regulation-by-regulation compliance is no longer sustainable as regulatory frameworks grow more overlapping and data environments more distributed. A holistic approach — anchored in shared controls for access management, data protection, and auditability — allows organizations to satisfy multiple obligations through a single framework while preserving the specific requirements of each regulation. Achieving this requires cross-functional collaboration among legal, IT, security, and risk teams, and security controls built from the outset to support transparency and adaptability. Organizations that centralize compliance management into a unified Zero Trust, data-centric model are better positioned to respond to regulatory change without disrupting core business operations.
For more detailed exploration of the technical framework, case studies, and NextLabs solution, read the full white paper.






